Anyone with an iPhone is familiar with Apple’s cloud service known as iCloud. Anyone with an Apple account can use it for file storage, along with the option of buying extra storage space if necessary. The primary difference between the blockchain economy versus our traditional economy is decentralization.
Apple’s cloud service consists of storage space owned by Apple, making it centralized. Decentralization is at the heart of blockchain technology, and what it refers to is the nature in which authority and influence are structured within a system. Apple has complete control over every bit of storage that they give out, and can easily re-claim it if it chooses to.
Fortunately, there are decentralized alternatives that are not controlled by Apple, or any one entity for that matter. However, since iCloud is Apple’s service, the storage offered is owned solely by Apple; decentralized cloud services are owned by no one, so where does the storage come from? These protocols are in the hands of the participants within the system, so it is up to them to provide everything needed to operate a successful storage network.
Deals are made between clients and storage providers detailing how much data a client wishes to store away, and for how long. During the duration of the deal, providers must occasionally prove that the data stored away is still in their possession. Clients pay in increments throughout the contract until it has expired. The process of storing and retrieving data in a cryptographic manner can be both tedious and time-consuming, so it has been broken down into two separate positions: a storage provider and a data retriever. We’ll cover the two disparate roles and the steps they must go through.
Providers on the network are the ones who lend out their personal storage to clients and receive tokens for storing and verifying data over time. A provider’s potential to receive rewards is determined by how much storage is contributed to the protocol. Once data has been sealed and stored away, providers are selected to submit “proofs” of certain data within their arsenal.
There are two various types of proofs that must be submitted: Proof of Replication (PoRep) and Proof of Spacetime (PoSt). Proof of Replication deals with showing a unique encoding that is tied to a set of client’s data; by providing this coding, you’re stating that the information is still in your possession. Proof of Spacetime is a mechanism that performs window checks every 24 hours to make sure that storage providers are keeping up to date with client’s stored data. Instead of presenting a code for a specific piece of data, providers submit a daily PoSt of a specific sector within their arsenal.
Once an agreement has reached its end, a client’s files are sent back to them and at that point, the provider should have received full compensation for their efforts.
A retriever’s overall performance is based on the strength of their bandwidth; stored data files are retrieved through biddings that retrievers participate in. The winner receives the right to reclaim files for which they are compensated in increments as data is proportionately sent back to the client (again through the duration of an established agreement). Response time is a critical factor in succeeding as a retriever, the faster your responses, the better your reputation.
While there is lucrative potential in contributing to storage networks, it is a highly technical occupation requiring expensive and complex hardware. Similar to mining Bitcoin, storage providing consists of solving cryptographic equations.
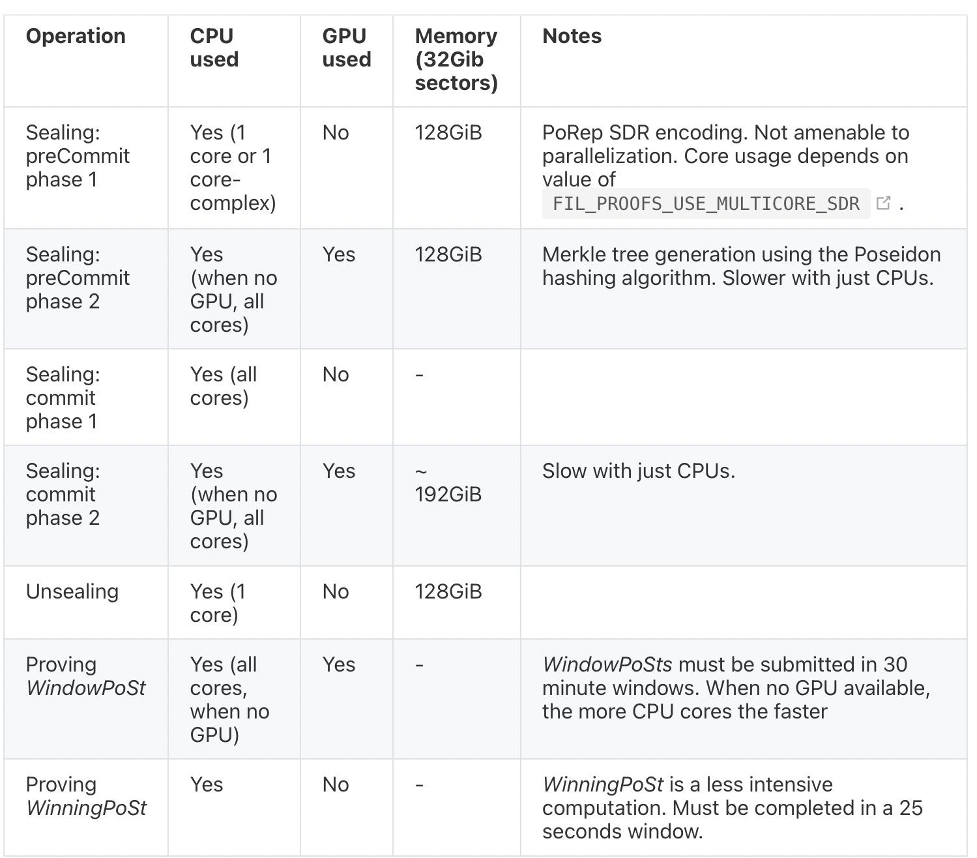
Apart from storage, network contributors must have either a central processing unit (CPU) or general processing unit (GPU) to assist in solving such equations. There’s additional hardware needed as well depending on the operation taking place on the network.